Detecting and Dismantling Botnet Command and Control Infrastructure using Behavioral Profilers and Bot InformantsSponsored by Department of Homeland Security (DHS) Science & Technology (S&T) Directorate |
Project Summary:
Global Internet threats are undergoing a profound transformation from attacks designed solely to disable infrastructure to those that also target people and organizations. At the center of many of these attacks is a large pool of compromised computers located in homes, schools, businesses, and governments around the world. Bot software enables criminals to remotely control each infected system and group them together to form large attack groups called botnets [1].
In this project we are developing and deploying a system to detect and dismantle botnets. Our approach is motivated by an understanding of the complete botnet life-cycle rather than a single botnet feature. Bots are fundamentally different from previous Internet threats because they have a command and control channel which makes them infinitely adaptable. We believe no single detection approach will successfully mitigate the threat of botnets. Instead we will deploy a system that detects bot behavior rather than specific bot symptoms. This more comprehensive approach means quicker detection and adaptability as attackers attempt to evade the system. The system is also based on existing network security standards like NetFlow, DNS data, darknet data making it easily deployable and maintainable.
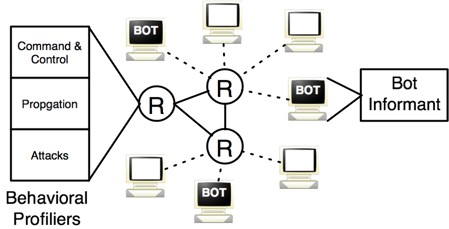
Our proposed architecture, shown below, consists of two main components:
- Behavioral profilers are a simple, robust approach to detecting botnets that build on proven techniques, such as IRC-based detection. Three individual profilers are used to detect all phases of the Botnet life-cycle including; propagation detection based on several kinds of scan detection, command and control detection based on control signatures and rendezvous detection, and multi-sensor attack detection based on ddos and spam detection.
- Bot Informants: To gain additional intelligence on the means, motives, and membership of bots and bot controllers we make use of Bot informants which are undercover agents that work to infiltrate and then assist in dismantling botnets.
[1] Evan Cooke, Farnam Jahanian, and Danny McPherson. The Zombie roundup: Understanding, detecting, and disrupting botnets. In Proceedings of the Steps to Reducing Unwanted Traffic on the Internet (SRUTI 2005 Workshop), Cambridge, MA, July 2005.